What is xdecrypt.com?
I’ve noticed that my page about xdecrypt.com has picked up quite a lot of traffic with people asking the same question, so I’ve decided to write this to post to explain what xdecrypt.com is.
Whenever you logon anywhere with your username or email address and password that site has to store those details to make sure you are who you say you are. In storing those details you have to make sure that they are safe from prying eyes.
For instance lets use Facebook as our example. You logon with your email address and your password. There is a danger when you store peoples passwords that someone could get access to that file and have all the passwords for all your users which is really not good.
So in order to get around storing passwords in what is described as “plain text” (ie you can look at the file and know the password), computers do something called a “Hash Function“. In a basic form this is a mathematical formula which changes your password into something not readable and stores that value.
Now here’s the clever bit. The mathematical formula is that good that every single different password has a completely different hash value. I’ve converted two words “password” and “Password” (notice the capital?) into MD5 hash.
- dc647eb65e6711e155375218212b3964 = Password
- 5f4dcc3b5aa765d61d8327deb882cf99 = password
They both look completely different and thats the beauty of it. Those two very similar passwords look totally different.
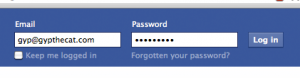
Back to our Facebook example, so Facebook stores your password as a Hash function in it’s database. You type in your username and password, Facebook converts what you’ve typed in as your password into a Hash, if that Hash and the stored Hash are the same it will let you login. All done without storing your password as plain text.
This is where xdecrypt.com comes in. If you go on the site and copy and paste those two hashed strings, they’ll give you the password. Xdecrypt.com is a huge database full of what password goes with what hash.
So who uses xdecrypt.com? Probably lots of people. System administrators can use it to test their passwords are secure, guys who write software can use it to make sure that their systems are secure. Bad guys may use it if they get a whole pile of hash values they need to reverse engineer.
There is more to it, hashing is a part of cryptography, and cryptography is a huge subject area. In our Facebook example above there are steps that they have taken to prevent you from doing just what I’ve written. It’s by using a processes call “Salt“. That still doesn’t mean you should relax when it comes to passwords, you should try to have complex passwords involving letters, numbers and punctuation.


35 Comments
Why is my name ‘tatelyncollis’ in xdecrypt.com?
I can’t give you a definitive answer but can give some hypothesis.
1) Someone at some point has hashed your name on xdecrypt.com.
2) Xdecrypt.com may use a web crawler to come up with strings to hash and add them to their database.
Should you be worried that your name is in xdecrypt.com? No, I wouldn’t be. Your username isn’t sensitive as your passwords are and isn’t really worth protecting the same as your passwords. Make sure you keep your passwords complex and hard to guess with numbers, letters and punctuation marks.
Are you worried that your name is in Google at all? Probably not, and it’s the same logic if it’s hashed or not.
Thanks for visiting Tatelyn 🙂
Gyp, my question is probably similar to the one as Tatelyn’s but, are hackers and xdecrypt related in the sense that…hackers use this to decode your hash and find out your password?
Hi Dave,
Short answer is yes they could be.
However hackers won’t be the only group using it xdecrypt like this. Also many passwords on various websites have various other security applied to them (see about Salt in the main post), in order to make resources like Xdecrypt less useful.
However, if you’re asking this question because your password has shown up on Xdecrypt I would recommend you change it immediately. It’s no longer secure from dictionary attacks which would negate the use of Salt. Try a complex password with upper and lower case letters, punctuation and numbers 🙂
Thanks for dropping by, and if this hasn’t answered your question let me know and will do what I can.
Gyp
Gyp,
This defininetly makes a lot of sense. If i can, i’d like to as a couple more followup questions. One is, how can i go about making sure that no one can just take my hash and convert it to find my password. Meaning, what would be the best security precaution to do this. I understand changing your password, as you mentioned, does a great deal in helping make less use of xdecrypt.com. Also, how do these hash’s get out in the first place? To me, the only way one could put these hash’s here is the website administrator. Coming to my last, this may be a dumb question but I really want to know the answer. Do websites security logins differ from others? Meaning, does a say…game forum security login differ from that of a bank? The answer is probably yes but, if that’s the case, is it fair to say that it is “more difficult” to obtain a hash from a bank then it is from a gaming forum or website? I know I’m asking a lot of questions but I really want to know the truth of all this. My last question is, yes my password has come across xdecrypt.com but it’s from an old forum website and I don’t really care…the one that took my hash and password, can they access my computer as well or just the forum? Thank you very much Gyp.
Hi Dave, will help out how I can 🙂
The first thing to bear in mind is that xdecrypt doesn’t actually decrypt your hashes mathematically, it only stores the hash and corresponding password. In other words it gets a whole pile of words, converts them to hashes and thats it. It then stores the hash and the word in a database. I know it’s a subtle difference but it is important.
1) Securing your passwords
The best way is to make each hash completely unique. Therefore if someone gets your hash, and it happens to be on a site like xdecrypt then they’ll only have the password to that one site. There are some quick and easy tricks that helps you make this even more secure.
Say for instance your password is “abracadbra1973”. If I used it on a site called “companya.com” I could make my password for that site “companya.com.abracadbra1973”. So therefore if the website administrator typed in the hash of my password from the companya.com website, they wouldn’t have much to go off. It’s like salting your passwords yourself and is a quick and easy solution.
Bear in mind though if a website doesn’t keep your password hashed in their database then the above steps won’t help someone to figure out your password for other sites if you used the same “abracadbra1973”.
There are also programs that will generate unique and secure passwords then keep a secure record of them try http://sourceforge.net/projects/keepass/. The problem I have with these is that if you’re not on the computer where the program is you won’t be able to log on to any of your websites.
2) How do Hashes get Out
It’s unfortunate that websites get hacked. Sloppy practice by website owners, unscrupulous website administrators trying their luck with their member details, bad guys hacking in and getting the details are all ways hashes can be released. All naughty, but unfortunate. Some massive brands have been hacked lately (thinking Sony mainly), and all these can lead to problems.
I don’t know how xdecrypt get their words to hash, but I have a feeling they probably use a web crawler that scans the internet for words and uses them.
3) Do Banks have Better Security than Game Websites
I’m confident that they do. I don’t know for sure, but I could imagine that banks are the best at doing things like salting security information. Also my bank gives me for all intents and purposes 3 different passwords, parts of all three of which I need in order to logon. This is all to do with authentication.
But I dare say the answer to your question is yes, bank security does differ from game forum security (in my experience). You’re right I dare say obtaining a hash from a bank is going to be an awful lot more difficult to get than from a game forum. The bank has no doubt other security measures to protect from just this risk.
4) Your Password on Xdecrypt
I think you’ve answered your own question 🙂 If that password was only used on an old forum, and you DON’T use that password any more or anywhere else you have nothing to worry about. Yes they can only access that forum, that is if they know your username or email address as well.
Can they access your computer? I’d say no. I dare say your computer is behind a firewall and that is your main security. Also just say you had the same password to logon to your computer that you had on the forum. The only way that they’d be able to use your password is if they sat down in front of your PC and typed it in. Also bear in mind that if all someone has got to go off is your username and hash and password, figuring out who you are and where your computer is will be quite difficult.
There is an awful lot more to security (which is where this question leads to), but I dare say you’d be safe. But again, if your password has shown up in Xdecrypt, change it!
If this doesn’t answer your questions let me know and will see what I can do to explain better 🙂
Gyp
Gyp,
Thank you, you’ve answered all of my questions 🙂 I appreciate it a lot and thanks for the referral to the unique password program I’ll definitely give it a go. If i have any more questions, you’ll be the first I’ll reference!
Thanks again,
Dave
No problem at all Dave, glad to help. Feel free to come back with any questions 🙂 Gyp
hey gyp
i have some questions…
1- If i found my name here in the database is that mean that some one try to hack my account somewhere?
2- Why my name is repeated many times and everytime have different hash (i understand that for the same text have different hash)?
3- How could i know if this hash is for my name or my email or my password ?
i.e: like for example
•dc647eb65e6711e155375218212b3964 = my name or my password
how could i know?
4- Is there anyway to delete the hash or block my name?
5- Should i be worry that my name is here in the database?
Thanks alot.
Hi Brian,
I’ll help how I can 🙂
1) Name on Xdecrypt
I dare say it probably doesn’t mean you’ve been targeted to be hacked into. What it more likely means is that the web crawler that Xdecrypt use has come across your name on a forum, website or other such resource somewhere. Just because your name is on Xdecrypt it doesn’t mean you’ve been hacked or can be hacked, and in my opinion it has a very small impact on your online security.
2) Name Repeated
This could be one of two things. Firstly your name has been hashed using different techniques (ie MD5 and SHA1) and these are different mathematical formulas that you can use. Or, if your name is slightly different, for instance “John Henry” will give a completely different hash to “JohnHenry” or even “john henry” (notice the capitals and spaces?). If you’d like to fill in a contact request with specifics of the name I will give you a definitive answer on this one.
3) Recognising Hashes
The only sure way to know what the hash refers to is to use a site like Xdecrypt 🙂 Thats the beauty of the site. It tells you the plain text from the hash. The other method is to hash the string yourself and search for that. If you want to keep your information off of Xdecrypt DO NOT USE THE HASHER ON XDECRYPT, Google “online hashing” or similar.
4) Deleting Data from Xdecrypt
Yes, you can request a hash is deleted from the Xdecrypt database, click for Xdecrypt removal.
5) Should you be Worried?
My real name, and my alter-ego Gyp is on Xdecrypt, and I’m not worried in the slightest. My name isn’t confidential, it’s my passwords that are.
If you have any other questions don’t hesitate to get in touch, and if you want specifics for your third answer drop me a line 🙂
Gyp
Thanks a lot Gyp :))
No problem at all, glad to help 🙂
I see some people have a similar issue, but I’m a little unclear. I found my full name on it (much like Tatelyn), but I don’t have any passwords like that. Does that mean someone else has my name as their password ? Lol
Hiya Wise, thanks for dropping by, and I’ll try and help clarify how I can 🙂
I suppose someone could have your name as a password, after all stranger things have happened.
But I dare say like Tatelyn the reason your name appears on xdecrypt is because the programs that they use to come up with things to hash found your name somewhere on the internet. I wouldn’t worry, if your name appears on the internet any how it being hashed or not doesn’t make a great deal of difference.
If this doesn’t clarify it let me know and will try to explain differently.
Hi gyp,
Its nice to see you helping with the hash codes. My question might be a little out of the context though it concerns the passwords. I have a friend who has lately been harassed by tempering her facebook account by a friend. My question is, what are the key ways that allowed such hacking? (the hacker sits in another country)
Hi cht, thanks for dropping by.
If I understand your question correctly in that someone is logging onto your friends’ Facebook as her? In my experience the way which someone could access their Facebook would be:
A) Know their email address and password
B) Have full access to their registered email address so they could change the password
C) VERY unlikely chance but if they had access to your friends computer they could use the cookies if they login automatically
D) Although I have recently heard about a virus specifically stealing people’s Facebook login details your example does seem to be rather targeted and rules this one out
E) Another way is that if someone had managed to get a hold of Facebooks user login data and had reversed their hash table. Again this one is unlikely because no doubt Facebooks security in this regard is likely to be similar to a bank. If this has happened I am very surprised it hasn’t been on the news.
It is possible if your friend uses te same username and password on various sites then another site could have been compromised meaning they have your friends details.
Hope this helps and tell your friend to change her password 🙂 If you need more help let me know.
Gyp
Hi Gyp,
I see my name on your site, can you tell exactly me how it got there please?
What is the purpose of your site? (In lamons terms please)
How do I put that code on facebook? Where do I enter it etc?
I can’t seem to comment
Thank you
Hi Wayne,
Thanks for dropping by, I will help how I can.
Your name on my site? I have nothing to do with Xdecrypt.com other than having written a couple of posts on my blog about their site. If you mean why is your name on Xdecrypt.com then I don’t know 100%, but they have a list on their website where they get their data from. I’ve searched my site here, and the only details I can find relating to you is your comment 🙂
What is the purpose of Xdecrypt.com? It is a list of words and how they look once they have had a mathematical formula applied. It’s purpose (from my perspective) is to assist with ensuring secure practice, and to act as a catalyst to make the internet a more secure place for all of us.
If you mean what is the purpose of Gyp the Cat dot Com then it is my own personal blog where I write about subjects that interest me, usually with a bias towards business and information governance.
As for the codes from Xdecrypt.com you cannot put them in yourself to websites. Facebook for instance takes what you type in and performs a mathematical sum to it. So you can’t type the hashes in directly (since it will hash the hash!) that is why it’s a secure way of protecting you data.
As for you don’t seem to be able to comment I think you fixed that one 🙂
Sorry I can’t be any simpler, it is a rather complex subject area, but if I can be of any more help please let me know.
Gyp
So how did my name get there in the first place?
Hi Violet, thanks for your comment.
I don’t know for sure, but xdecrypt.com appears to use a web crawler to come up with words to put on their site, so if they found your name on the internet somewhere they added it to their website.
Gyp
Thank you 🙂
Just one more question.
Besides testing passwords. Why show this stuff on the internet where everyone can see?
A very good question that one Violet, why put this online. I’d imagine the guys at Xdecrypt.com are enthusiastic at making sure people use good passwords and people who develop websites and computer software are enthusiastic about maintaining good security too.
I’ve read also that Xdecrypt.com was started as a University project, so it could be to get them good grades in their course 🙂
I know this isn’t a complete answer, but I suppose you could ask why put anything online.
Hope this helps,
Gyp
Oh I see! I guess I should say good on them ^^
Thank you!
I’m amazed that this site has not been shut down yet, although it appears it can be used educationally, this it is a very thin veil of supposed credibility when all this site is doing is making it easy for people to hack me and my details.
Information like this should NOT be made freely and publicly available and both this xdecrypt and “Gyp the Cat” should be shutdown. I have taken this up with Federal law enforcement.
Hi Carl,
Thank you for visiting, I can appreciate your thoughts on this subject.
In my opinion the thing to bear in mind here is that anyone given enough technical ability can produce a site like Xdecrypt, and Xdecrypt isn’t the only site that provides Rainbow Tables and Hash Tables online. Also given the same amount of technical ability you could produce all this data and not put it online.
I am still a firm believer that if people who make programs deal with security the right way then sites like Xdecrypt are pretty much useless. See my comments about Salt.
As for the legality of the situation I am not a lawyer, nor do I consider myself a legal expert. But my limited understanding of the legality of sites like mine and Xdecrypt may change dependant on the jurisdiction. I know some countries have strict rules governing how Encryption is used, and if it’s suitable for use in other countries (exporting encryption).
Taking this into account and in my experience, the methods of cryptography that Xdecrypt use are available worldwide and ship by default with a lot of computer software. I would have thought that this fact alone makes the encryption in use by Xdecrypt legal in most jurisdictions. But again I do not consider myself to be an expert on such matters.
Thanks again,
Gyp
Dear Gyp,
how can I try all this on Facebook? Can I convert my password in hash and type the hash in the place of the password?
How do i know if it is a MD5, Sha1, etc.?
How do you convert a password into hash? is it a program?
Your site is very interesting, it is helping me to understand this weird computer world!
Thank you!
Hi Barbara,
Happy to help 🙂
You can’t type in a hash of your password into Facebook. Whatever you type in as your password is hashed, so if you did this you would be hashing a hash. This is part of the security, since the hash is a repeatable mathematical function it is a safe way to store passwords. It also means that obtaining the hash won’t result in getting the password.
The main difference between MD5 and SHA1 looking at them is an MD5 hash is 32 digits long, and SHA1 is 40 digits long. Mathematically they are very different.
Just about every modern computer programming language and computer operating system has some sort of hashing functionality built in. Microsofts C# for example supports all the major (and minor) hashing methods. This site allows you to create a hash online. I’d be careful what you type in though, I can’t guarantee that what you type in there won’t end up on somewhere like xdecrypt.com.
The best thing you can do is to use secure passwords (ie letters, numbers and punctuation marks), and use different passwords for different sites.
Gyp
Thank you!
But i am sure a hash can be very useful, what can i do with it?
Don’t worry, I am not going to type my password on hash online!
I can’t think of any useful things to do with your hash. I suppose if you knew the hash of your password you could make sure if it ever shows up on Google then it means you need to change it 🙂
A hash is very useful to protect your password, especially if programs or websites also use a salting function on your password too!
Then i will look if my pw shows up!
Thank you, have a nice evening
Oh sorry, hope you don’t mind another question! This internet codes are charming!
I noticed that in the list of hash words and equivalent plain text, there are some names of people, wich are composed of two words (i.e. John Smith or Linda Jones). They are transformed into hash codes too. Are these passwords? I only know passwords should be 1 word without spaces, how is it possible somebody used it as a password?
Well i hope they didn’t use their own name as password!
Thank you again dear Gyp!
Hi Barbara,
Sorry for the late response, I have been very busy. Your password can technically be anything you want it to be, you can have spaces in a password very easily. A password with spaces may be more secure than one without 🙂
From a hashing perspective a space is as much a character as any other letter, number or punctuation mark.
Gyp
Thank you dear Gyp!
I am sure my passwords will be more secure from now on.
Many blessings!
Hi Gyp,
I was online last night and I decided to Google my email address and YEP my name was on the xdecrypt website. Now before last night I didn’t even know these things were possible ( which made me realize I have to educate myself a little more on internet security) So I write to you because after reading some of your post I had some questions. You seem very knowledgeable and I really like the way you advised others, you’re wrote very professional and seem down to earth so beforehand. Thanks in advance 🙂
So what exactly is a string?
How do I get that?
I know a hash is a form of encryption created from information put on the Internet. right?
Is a string, a function in my computer, or do I go to a website to create one?
Does a string then convert into a hash?
I’m a bit clueless on the subject but eager to learn so any help would be good. Do you recommend any books I can read to further educate myself on these things. What is this called anyway lol encryption? idk
Thanks Again,
Zu
Hi Zu,
Thanks for stopping by I’ll help how I can 🙂
A “string” is a computer programming term which describes (basically) anything that you can type in using your computer keyboard. So when we’re talking about hashes and xdecrypt, it just refers to the letters/numbers/punctuation/spaces that you can use for your password or username. In this case a string will be your name you’ve found on xdecrypt.
A hash just isn’t used for the internet, it’s something that used in computers in general. It’s a popular and good way to secure things on the internet since you store your details in a way that makes it difficult to get the information back again. A hash is also used a lot for making sure your computer works, for example your anti-virus program will use hash functions to make sure your files are safe and they haven’t change unexpectedly.
So from a string (bearing in mind it can be anything you can type in with your keyboard), you apply the mathematical formula to it, then it becomes a hash.
As for further reading, encryption is a subset of cryptography, if you want an introduction to encryption try this encryption tutorial. Hashes could be described as a subset of encryption! So they’re all very closely related, you may be best off starting looking at Cryptography.
If you’d like any more help don’t hesitate to ask 🙂
Gyp